February 2019
Firefox flextrail MTB review
I got my first MTB firefox cyclone in 2010. I am still having cyclone and it is in good condition. I thought to upgrade to a better MTB now. I am using firefox cyclone since quite a long without any glitch so I decided to find new MTB from same brand. This time I was […]
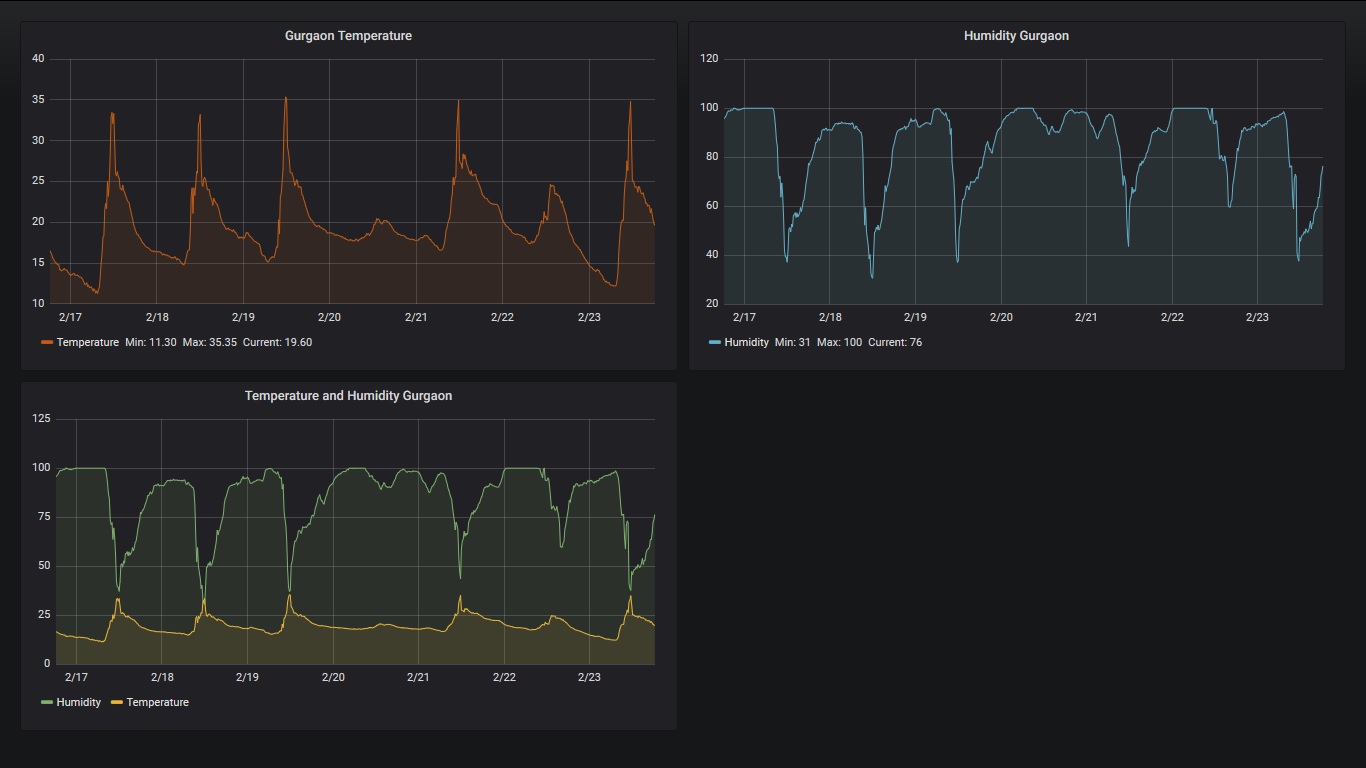
Publish IoT data in Influxdb and visualize in Grafana
I had build an IoT enabled weather station. Now let us build a nice platform to store time series data coming out of DTH22 (weather sensor) on NodeMCU and visualize it into Grafana. I have installed and configured influxdb and Grafana onto my raspberry pi which also hosts my MQTT broker. Weather station code transmits […]
Secure Elasticsearch and Kibana access using Apache reverse proxy
Default ELK installation may not fulfill enterprise requirements as kibana, the visualizer, works on port 5601 without any authentication and elasticsearch listens only on loopback IP on port 9200 without any authentication. You may want to run kibana on standard http/https port ie 80/443 with authentication control. Similarly, you may want to allow elasticsearch access […]
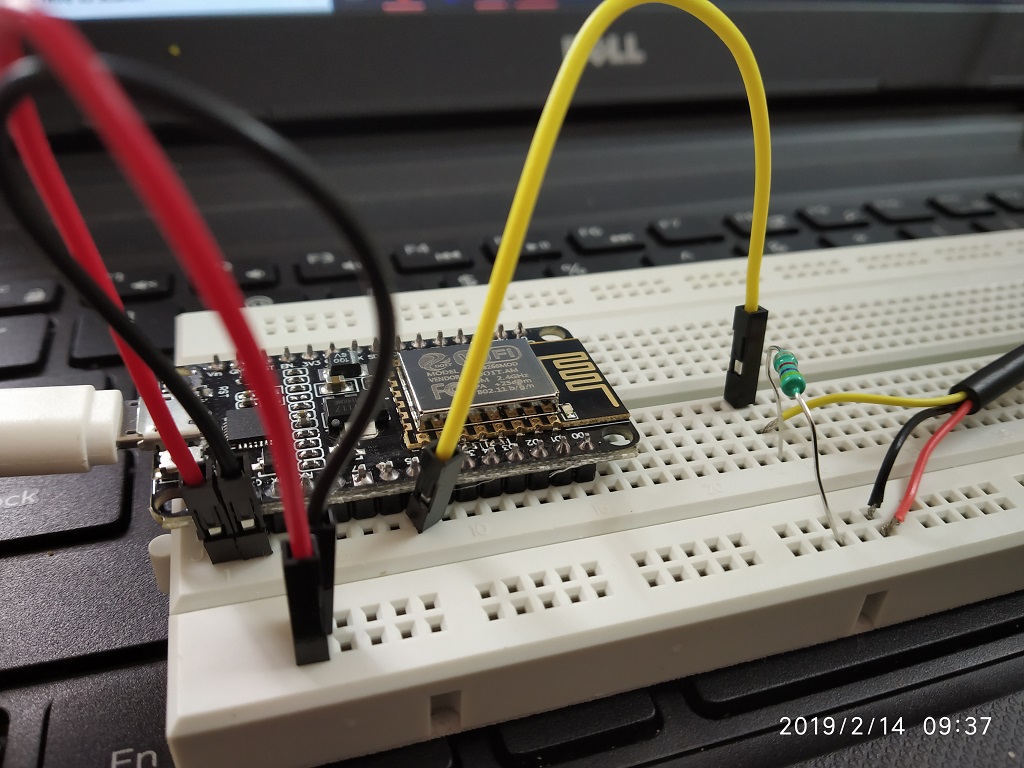
Monitoring aquarium temperature using DS18B20
I have a aquarium with two parrot fishes and few other species. Parrot fishes live happily within 25 to 32 degree Celsius. If temperature goes out of limits then it effects metabolism and behavior of fishes. Even though aquarium heater has thermostat I thought to observe temperature and record it over time. For this you […]
Querying elasticsearch with REST json
You may like to read ELK installation and configuration and ELK with syslog and SNMP before this. Recently I was looking to build some useful queries to search elasticsearch database having syslog messages from my syslog-ng servers. My requirement was to pull records within datetime ranges matching with set of hosts/IPs and text patterns within […]
Create a simple CA to sign SSL certificates
Securing traffic on various apps in organizations or even in a small home lab is very important to protect passwords and other critical information floating on LAN or WiFi. Let us build a handy CA in simple steps to generate own certificates which can be used in internal applications. Before this you may also like […]